-
Defensive Secuirty Intro
Defensive Security Intro Introducing defensive security and related topics, such as Threat Intelligence, SOC, DFIR, Malware Analysis, and SIEM. Task 1: Introduction to Defensive Security Intro n the previous lesson, we learned about offensive security, which aims to identify and exploit system vulnerabilities to enhance security measures. This includes exploiting software bugs, leveraging insecure setups, and…
-
Offensive Security Introduction

Hack your first website (legally in a safe environment) and experience an ethical hacker’s job. Task 1: “What is Offensive Security? “To outsmart a hacker, you need to think like one.” This is the core of “Offensive Security.” It involves breaking into computer systems, exploiting software bugs, and finding loopholes in applications to gain unauthorised…
-
Hello World!
-
Best suitable software for ethical hackers (for beginners)

Ethical hacking is a sanctioned endeavor to gain unauthorized access to a computer system, application, or data by employing the techniques and methodologies of hostile attackers. This practice is instrumental in identifying security vulnerabilities, which can subsequently be rectified before a malicious attacker has the chance to exploit them. It is important to recognize that…
-
Step-by-Step Guide to Setting Up Virtual Machines

What is a Virtual Machine? A virtual machine (VM) is a software-based emulation of a physical computer, designed to function similarly to a tangible system while utilizing virtual resources in lieu of physical components. VMs facilitate the establishment of isolated environments on a host computer, enabling the execution of programs, operating systems, and various other…
-
Understanding One-Time Passcodes for Online Security
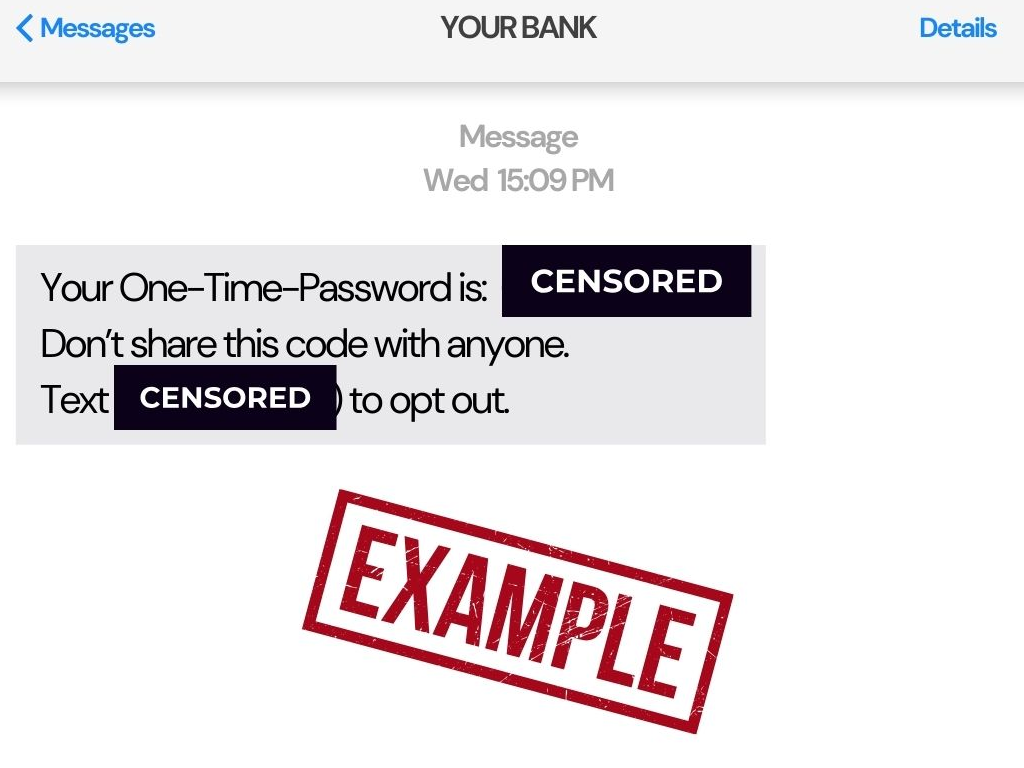
OTPs, or one-time passcodes, are numerical codes that are only valid for one login attempt or transaction. They serve as a crucial layer of security in various online platforms, protecting users from unauthorized access by confirming their identity. OTPs are a common way to verify accounts and secure online transactions, especially in banking, e-commerce, and…
-
The Hacker Spectrum: Who Are Black, White, and Grey Hats?

If you keep your eyeballs glued to the news and have a fascination for all things techy, you’re familiar with the term “hacker.” But did you know that these digital cowboys come in various flavors, like black hat, white hat, and gray hat? Yes, just like your quirky uncle’s three favorite kinds of cheese! The…
-
Exploring Kali Linux: The Ultimate Tool for Cybersecurity Enthusiasts
Kali Linux has become a buzzword in the realm of cybersecurity, and for good reason. This powerful operating system is a favorite among ethical hackers, penetration testers, and security researchers. In this article, we’ll explore what Kali Linux is, its key features, and why it has gained such popularity in the IT community. What is…
-
Preventing Future Cyber Incidents: CrowdStrike Case Study

In July 2024, CrowdStrike experienced a significant incident that led to a global IT outage, affecting many clients and raising serious concerns about cybersecurity practices. This analysis delves into the findings from CrowdStrike’s Root Cause Analysis (RCA) report, shedding light on what transpired, the underlying causes, and the lessons learned. Overview of the Incident On…
-
Best System Configuration Tools for Secure IT Environments: A Comprehensive Guide

In the rapidly evolving world of cybersecurity, having the right tools at your disposal is crucial, especially for those new to the field. System configuration tools play a vital role in managing and securing IT environments by ensuring systems are correctly configured and vulnerabilities are minimized. Here, we explore some of the best system configuration…
